Blockchain security is a complex interplay of cryptographic techniques, consensus mechanisms, and network protocols. Each component plays a critical role in safeguarding digital assets and ensuring system integrity. Understanding these elements is essential for recognizing vulnerabilities that could jeopardize trust in decentralized networks. As the landscape of blockchain technology continues to evolve, the implications of security measures become increasingly significant, raising questions about their effectiveness and adaptability in a rapidly changing environment.
The Role of Cryptography in Blockchain Security
Although blockchain technology is often lauded for its decentralized nature, the underlying security mechanisms primarily rely on cryptographic principles to ensure data integrity and confidentiality.
Cryptographic keys secure transactions, while digital signatures authenticate users, preventing unauthorized access.
This intricate interplay of cryptography not only safeguards information but also upholds the fundamental tenets of freedom and autonomy within decentralized networks, promoting trust among participants.
See also: newsgigacom
Consensus Mechanisms: Ensuring Trust in Decentralized Networks
How do decentralized networks maintain integrity and trust without a central authority?
They utilize consensus mechanisms such as proof of work and delegated proof to validate transactions.
Proof of work requires significant computational effort, deterring malicious actions, while delegated proof enables selected participants to validate transactions, enhancing efficiency.
Together, these mechanisms foster trust and security, ensuring decentralized networks operate effectively and transparently.
Network Protocols and Their Impact on Data Integrity
As decentralized networks evolve, the protocols governing their communication and data exchange play a critical role in maintaining data integrity.
Network scalability often introduces protocol vulnerabilities, potentially compromising the trustworthiness of data transactions.
Understanding these vulnerabilities is essential for developers and users alike, as even minor lapses in protocol design can lead to significant breaches, undermining the foundational principles of decentralized systems.
Best Practices for Safeguarding Your Digital Assets
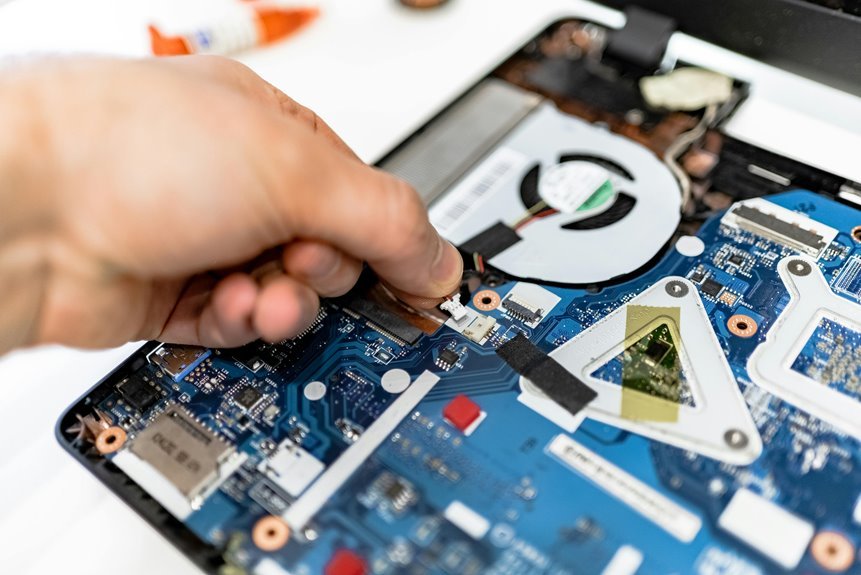
While the decentralized nature of blockchain technology offers numerous advantages, it also necessitates the implementation of robust security measures to safeguard digital assets.
Adopting best practices, such as utilizing hardware wallets for enhanced wallet security and securely managing private keys, is essential.
Regularly updating software and employing two-factor authentication further fortifies defenses, ensuring that users maintain control over their digital wealth in an increasingly vulnerable landscape.
Conclusion
In the intricate tapestry of blockchain security, cryptography serves as the unbreakable thread, weaving trust and integrity throughout the network. Consensus mechanisms act as the vigilant sentinels, ensuring that every transaction is validated and embraced by the community. Meanwhile, robust network protocols form the sturdy foundation upon which digital assets rest. By adhering to best practices, users can fortify their defenses, transforming their digital wallets into impenetrable fortresses against potential breaches in this ever-evolving landscape.